Published on:
10 min read
Why Secure Software Downloads Matter More Than Ever
Downloading software used to feel routine: click the first result, hit install, and move on. That habit is now risky. Modern attackers no longer rely only on obvious viruses or suspicious email attachments; they increasingly hide malware in fake installers, poisoned search ads, cloned download portals, and compromised software packages that look completely legitimate. For individuals, that can mean stolen passwords, drained bank accounts, or ransomware. For businesses, one careless download can trigger data loss, downtime, compliance violations, and major reputational damage. This article explains why secure software downloads have become a frontline cybersecurity issue, how software supply chain attacks and counterfeit installers work, what warning signs people miss, and which practical habits sharply reduce risk. If you install apps for yourself, your family, or your company, these safeguards are no longer optional housekeeping. They are one of the simplest, highest-impact defenses you can put in place today.

- •The download button has become a security decision
- •How attackers weaponize fake installers and compromised packages
- •What a single unsafe download can cost individuals and businesses
- •The safest places to download software and the red flags to watch for
- •A practical checklist for secure software downloads at home and at work
- •Key takeaways: the habits that make software downloads safer
The download button has become a security decision
For years, software downloads felt like a low-risk task. If a website looked polished and the app name was familiar, most people assumed the installer was safe. That assumption no longer holds. Attackers have shifted toward tactics that exploit trust, not just technical weakness. Instead of trying to break into your device directly, they trick you into inviting them in through fake installers, repackaged apps, browser extensions, and poisoned update files.
The scale of the problem is not theoretical. IBM’s Cost of a Data Breach report has repeatedly shown that compromised credentials, phishing, and supply chain exposure remain among the most expensive and persistent attack paths for organizations. Meanwhile, consumer-facing threats have exploded through malvertising, typo-squatted domains, and fake “Download Now” pages designed to outrank legitimate vendors in search results. A user searching for a PDF tool, VPN, driver updater, or video converter is now part of an active threat landscape.
Why this matters is simple: software usually runs with meaningful access. Once installed, it can view files, capture keystrokes, read browser sessions, or establish persistence that survives reboots. One bad download can become a credential theft event, a ransomware incident, or a network foothold.
The pros of downloading from trusted, verified sources are clear:
- Lower malware risk
- Better patch integrity
- More reliable support and updates
- Hidden spyware or remote access tools
- Data theft that goes unnoticed for weeks
- Costly cleanup, especially on work devices
How attackers weaponize fake installers and compromised packages
The most dangerous downloads are often the ones that look normal. Attackers know users are suspicious of obvious scams, so they mimic legitimate software brands with surprising precision. A fake installer may use the correct logo, a near-identical domain name, and even a valid TLS certificate. To a busy user, it feels authentic enough.
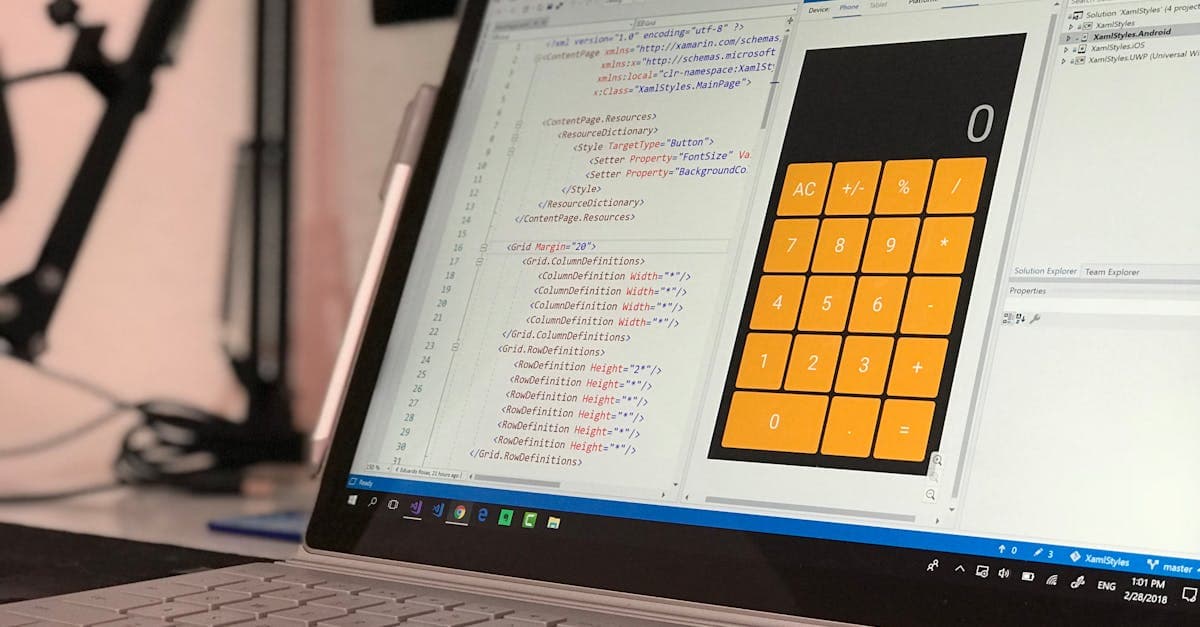
One common tactic is search engine abuse. Criminal groups buy ads or manipulate rankings so a fake download page appears above the real vendor site. Someone searching for Zoom, AnyDesk, OBS Studio, Notepad++, or even GPU drivers can land on a malicious clone and never realize it. Another tactic is bundling. The promised app may install, but it arrives with password stealers, browser hijackers, cryptominers, or unwanted remote management tools hidden in the background.
The threat becomes even more serious in software supply chain attacks. The 2020 SolarWinds incident showed what happens when trusted software distribution itself is compromised: attackers inserted malicious code into updates that were then delivered to thousands of customers. While that case targeted enterprises, the lesson applies broadly. Trust in the download process can be exploited at scale.
Key attacker methods include:
- Trojanized installers that include malware alongside real software
- Fake update prompts delivered through pop-ups or compromised websites
- Dependency poisoning in developer ecosystems such as npm or PyPI
- Cracked software and keygens that function as malware delivery vehicles
What a single unsafe download can cost individuals and businesses
People often underestimate software download risk because the consequences are delayed. The app may appear to install correctly, and the machine may work normally for days. Meanwhile, the malware steals browser cookies, copies saved passwords, or waits for the user to log into banking, payroll, or cloud admin accounts. By the time symptoms appear, the damage is already spreading.
For individuals, the most common costs are financial fraud, identity theft, and account takeovers. A fake utility app or cracked media tool can quietly harvest credentials from Chrome or Edge, then allow attackers to access email, shopping accounts, crypto wallets, and password managers. If multifactor authentication is weak or session cookies are stolen, even security-conscious users can be exposed.
For businesses, the stakes are higher because one infected endpoint can become an entry point into shared systems. In real-world ransomware cases, the initial compromise often comes from something mundane: a malicious installer, unauthorized remote access tool, or fake browser update. Once inside, attackers move laterally, escalate privileges, and target backups, file shares, and cloud services.
The upside of strong download controls includes:
- Fewer help desk incidents and device rebuilds
- Reduced ransomware and data exfiltration risk
- Better compliance posture for regulated industries
- Downtime that halts operations for hours or days
- Legal and notification costs after data exposure
- Erosion of customer trust that can outlast the technical recovery
The safest places to download software and the red flags to watch for
The safest software source is usually the vendor’s official website, reached by typing the known domain directly or using a trusted bookmark. For mobile apps, the Apple App Store and Google Play still carry risk, but they are significantly safer than third-party app repositories. For business tools, managed software catalogs, Microsoft Store for Business alternatives, and approved package repositories offer better control than letting employees search freely online.
Still, source alone is not enough. Users should verify the publisher name, inspect the URL carefully, and avoid download pages crowded with multiple misleading buttons. A classic warning sign is urgency: “Your player is outdated,” “Critical driver missing,” or “Download required to continue.” Legitimate vendors rarely pressure users with dramatic countdowns or pop-up scare tactics.
Practical red flags include:
- Misspelled domains or extra words added to a brand name
- Compressed files when an installer would normally be expected
- Requests to disable antivirus before installation
- Unsigned executables or certificate warnings during install
- “Free full version” offers for normally paid software
A practical checklist for secure software downloads at home and at work
The best defense is not one tool but a repeatable process. Most unsafe downloads happen when people are multitasking, solving an urgent problem, or trying to get free access to something quickly. A checklist reduces impulsive decisions and makes secure behavior easier to repeat.
Start with source control. Download only from official vendor pages, recognized app stores, or company-approved repositories. If you found the software through a search engine ad, pause and verify the domain independently. For workplace devices, avoid installing anything without IT approval, especially remote access software, browser extensions, driver tools, or file converters.
A practical download checklist looks like this:
- Confirm the exact website address before clicking download
- Verify the publisher or developer name on the installer
- Check for digital signatures or published file hashes when available
- Scan the file with endpoint protection before opening it
- Keep the operating system, browser, and security tools updated
- Remove local admin rights for everyday user accounts
- Back up critical data so one bad install does not become a disaster
Key takeaways: the habits that make software downloads safer
Secure software downloads are not about fear; they are about reducing avoidable risk in a world where attackers copy trust signals extremely well. If you remember nothing else, remember this: the most dangerous file is often the one that appears useful, urgent, and familiar. That is exactly why secure download discipline matters more now than it did even five years ago.
The highest-value habits are straightforward:
- Go directly to the official vendor instead of relying on search results
- Be skeptical of sponsored links for popular software and utilities
- Never install cracked software, unofficial activators, or random codec packs
- Check signatures, warnings, and publisher details before opening installers
- Limit admin privileges so a bad install has less room to cause damage
- Keep backups and security tools current in case prevention fails
Published on .
Share now!
LC
Logan Carter
Author
The information on this site is of a general nature only and is not intended to address the specific circumstances of any particular individual or entity. It is not intended or implied to be a substitute for professional advice.